For decades, cybersecurity has followed a simple, reactive formula: hackers find a hole, and we patch it. In the industry, we call this “The Cat and Mouse Game.” But in 2026, as AI agents become faster and grey-market, counterfeit hardware floods the global economy, simply reacting is no longer enough. The "mouse" has become too fast.
To protect our digital world, we must stop building higher walls and start playing the game on a different level. We need a strategy that is consistently 3 to 4 steps ahead.
The Failure of Passive Defense
Traditional security (firewalls, antivirus, and passwords) is what we call "Passive Defense." It’s a short-term solution. In regions where counterfeit devices are common, these official "safety stickers" mean very little. Hackers bypass them using everything from "Screen Overlays" that steal your PIN to AI voice cloning that sounds exactly like your family.
To win, we must move from reacting to a hit to breaking the hacker’s plan before they ever execute it.
The Proactive Blueprint: Four Steps to Dominance
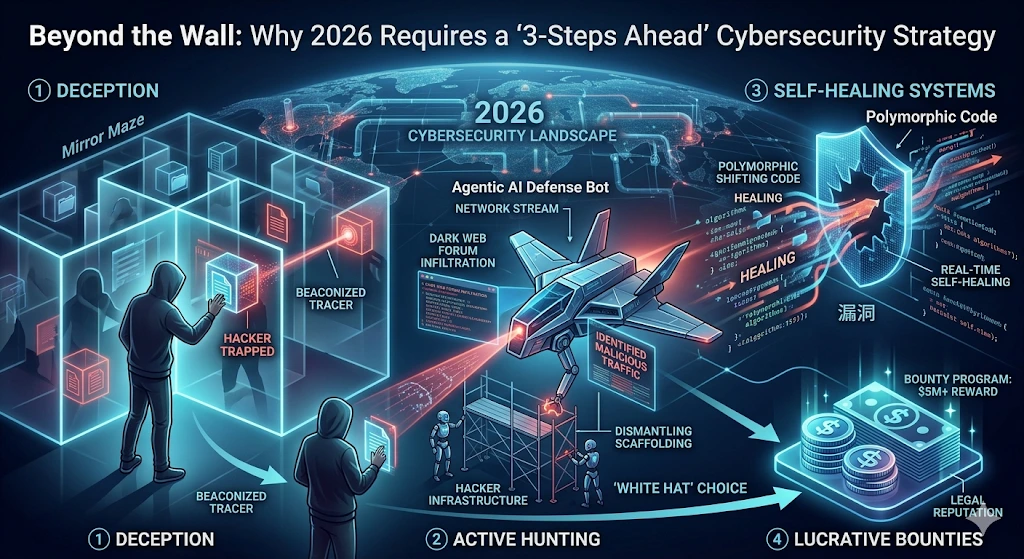
Step 1: Predictive Deception (The Mirror Maze)
Instead of just blocking hackers, we should welcome them—into a fake reality. By deploying "Honeypots" (fake servers) and "Honey-tokens" (fake files), we create a digital mirror maze. A hacker might spend days "stealing" data that is actually a tracking beacon. By the time they realize the data is fake, they’ve already revealed their identity to the authorities.
Step 2: Autonomous "Self-Healing" Systems
Human IT teams cannot work at the speed of an AI attack. We are now seeing the rise of "Polymorphic Code"—software that literally changes its own shape every few hours. By the time a hacker develops a tool to break into an app, the app’s internal structure has already shifted. It’s like trying to pick a lock that changes its shape while you’re turning the key.
Step 3: Turning Hackers into Heroes (Lucrative Bounties)
The best way to defeat an enemy is to make them your partner. Bug Bounty programs are reaching record highs in 2026, with some "Zero-Click" exploits fetching over $5 million. By making the legal payout more lucrative and stable than the "black market" price, we pull the world’s best talent into the light. We aren't just buying a bug fix; we are buying the talent so the enemy can’t have it.
Step 4: Active Threat Hunting
Security forces are no longer sitting behind a desk. They are now "hunting" inside hacker forums and dark-web channels. By infiltrating these groups with "Agentic AI" bots, we can dismantle a scammer's infrastructure from the inside before they even launch their first message.
The Bottom Line
In 2026, "perfect" security is a myth. The real goal is economic deterrence. By using deception, autonomous healing, and lucrative incentives, we make hacking so expensive, frustrating, and risky that it’s no longer a viable business.
The future of cybersecurity isn't about being unhackable: it's about being three steps ahead.